- You are here:
-
Home

-
Asian e-Marketing

-
July 2010

- Mobile Access of Handheld Devices Put Companies at Risk
-

Bilateral 5G roaming agreements will push global losses to $8 billion by 2028
A new study from Juniper Research has found losses from global roaming fraud are anticipated to exceed $8 billion by 2028, driven by the increase in bilateral roaming agreements for data-intensive use cases over 5G networks. In turn, it predicts fraudulent data traffic will account for 80% of global operator roaming-based losses by 2024.
-

Revealed: The most creatively effective digital & TV ads in Southeast Asia
The marketing data and analytics company, Kantar, revealed the winners of the 2023 Creative Effectiveness Awards in Southeast Asia, recognizing the most impactful ads of last year.
-

API Security Company Neosec acquired by Akamai Technologies
Akamai Technologies, Inc. announced entering into a definitive agreement to acquire Neosec, an API detection and response platform based on data and behavioral analytics.
-

GSMA report predicts tenfold rise in 5G mobile connections in Asia Pacific by 2030 as digital transformation gathers pace
5G will account for over two-fifths (41%) of mobile connections in the Asia Pacific (APAC) region by 2030, up from 4% in 2022, according to the GSMA's Mobile Economy APAC 2023 Report.
-

Appier integrates GenAI into its products to optimize key marketing applications for businesses
Appier announces that it has integrated Generative AI (GenAI) technology into three major marketing capabilities across its product lines. By connecting its advanced GenAI algorithms with OpenAI's ChatGPT language model, Appier can leverage the power of pioneering technology to help businesses increase productivity through advertising keywords and targeting parameters generation; intelligent conversational chatbot creation; and marketing copywriting and automatic content generation.
-

SentinelOne enhances cloud security with Snyk
Prioritizing which vulnerabilities to fix is a challenge for software developers, and the complexities of modern apps and the software supply chain have only made things more difficult. SentinelOne, a global leader in AI security, is partnering with Snyk, the leader in developer security, to ease the burden by integrating Singularity Cloud Workload Security, its real-time Cloud Workload Protection Platform (CWPP) with the Snyk Developer Security Platform.
-

5 Ways Earnest EQ Supercharges Marketing, Advertising, Branding & Comms Strategies
A 2023 Emotional Intelligence Market study citing “heavy growth” of $49.93 billion USD by 2027 exemplifies the extent to which mastering “EQ” versus IQ is taking brands to exciting new levels of success … and why not embracing EQ can result in extreme opportunity loss or, far worse, be an outright brand buster. This as today’s highly discriminating and demanding marketplace is seemingly rife with substitutable solutions. Whether the B2B or B2C sector, more often than not today’s consumers have alternate options—and they know it.
-

How AI will change the way we work in Asia Pacific
Microsoft introduced Microsoft 365 Copilot earlier this year, which will bring powerful new generative AI capabilities to apps millions of people use every day like Microsoft Word, Excel, PowerPoint, Outlook, Microsoft Teams and more.
-

Fastest web-based editor released for a new era of storytelling across streaming, broadcast, digital and social media
Dalet, a leading technology and service provider for media-rich organizations, announced the release of Dalet Cut, the cloud-native, real-time, lightning-fast multimedia and multiplatform editor fully integrated within the Dalet ecosystem.
-

Yahoo DSP advertisers now have access to low carbon PMPs
Yahoo and purpose-led ad platform Good-Loop announced a global partnership offering carbon neutral private marketplace (PMP) media opportunities to advertisers to help them become more sustainable.
-

New Study by MAGNA & Yahoo Urges Marketers to Pair Media Placement with Quality Creative in Order to Drive Stronger Ad Effectiveness
Media placement and creative work hand in hand when it comes to effective advertising strategies. A new study by MAGNA Media Trials and Yahoo set out to understand the role that creative quality plays in ad effectiveness, and the elements that contribute to quality creative. Creative, the Performance Powerhouse found that while media placement helps marketers find consumers where they are, creative quality was responsible for 56% of purchase intent, illustrating the strong performance of both tactics as they work together. The study suggests that marketers can greatly benefit from making small improvements to their creative in order to optimize ad performance, while also driving brand quality and trust.
-

Zero in with ABI’s Research Spotlights on research that is critical to your success
The global technology intelligence firm ABI Research just announced the release of Research Spotlights, suites of research focused on key technologies and trends within the vast ABI Research Library.
-

Plans for further integration of IBM watsonx with AWS
IBM announced plans to expand its relationship with Amazon Web Services to help more mutual clients operationalize and derive value from generative artificial intelligence.
-

New Apps, New Data, and New Resilience: Huawei Proposes Ways of Evolving Storage in the Yottabyte Era
The Innovative Data Infrastructure Forum (IDI Forum) 2023, revolving around the theme of "New Apps ∙ New Data ∙ New Resilience," took place on May 23 in Munich, Germany. The Forum brings together global industry experts and partners to explore the future of digital infrastructure towards the yottabyte era (a yottabyte is equal to a quadrillion gigabytes).



















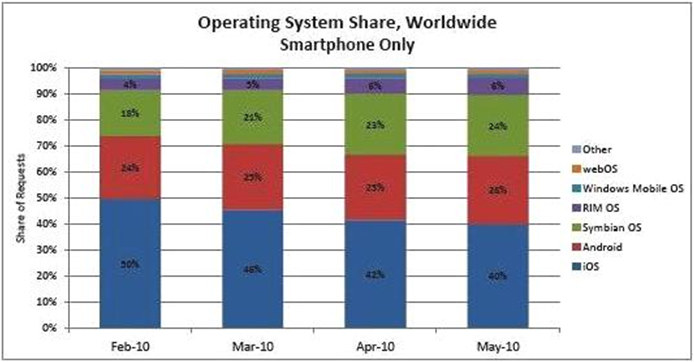
 Smartphones outsold laptop computers for the first time and the trend is likely to continue as many people acquired a taste to leave their laptops at home in favour of the smaller, lighter devices.
Smartphones outsold laptop computers for the first time and the trend is likely to continue as many people acquired a taste to leave their laptops at home in favour of the smaller, lighter devices.