- Category: August 2015 - Security
 “In today’s cybersecurity arena, the notion of using a traditional perimeter firewall as your primary line of defense is no longer the impenetrable wall it used to be, as hackers and malicious actors consistently find ways to sneak past the first trusted layer of defense”, states Thycotic, a provider of smart and effective privileged account management solutions. Rather, it even seems that the more security solutions and tools are deployed, the more vulnerabilities are introduced that can lead to network penetration, the company claims.
“In today’s cybersecurity arena, the notion of using a traditional perimeter firewall as your primary line of defense is no longer the impenetrable wall it used to be, as hackers and malicious actors consistently find ways to sneak past the first trusted layer of defense”, states Thycotic, a provider of smart and effective privileged account management solutions. Rather, it even seems that the more security solutions and tools are deployed, the more vulnerabilities are introduced that can lead to network penetration, the company claims.
Moreover, the combination of BYOD, distributed networks, mismanaged user access, and the sheer volume of external attacks have created a complex series of threat vectors that require unique defense-in-depth strategies, starting with inside the perimeter at the core of the infrastructure and working outward from there.
"Perhaps not surprising to those in the cybersecurity industry, it is apparent that for all the new defensive solutions that have been introduced, we still haven't cracked the code on how best to protect mission-critical data and company secrets. In fact, in some cases, we're only adding additional layers of complexity which provide attackers more attack vectors to use to break in," said Nathan Wenzler, senior technology evangelist at Thycotic.
In an effort to learn more about the methods, by which hackers are able to successfully break into and compromise enterprise networks, Thycotic sponsored an official poll at the conference venue in Las Vegas at Black Hat USA 2015, on August 5th that has been conducted live. The company secured 201 responses from both self-identified white hat and black hat hackers, and the results documented herein reveal some of the methods they use to infiltrate networks, and demonstrate the focus with which they target privileged account credentials.
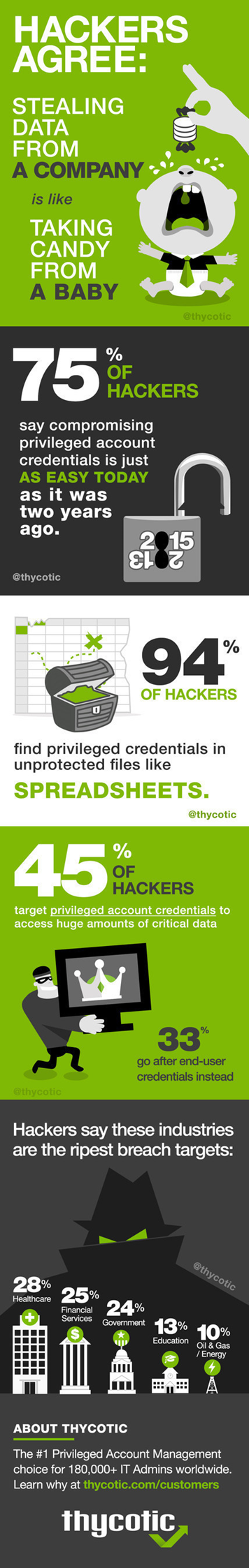
Interestingly, the survey revealed that a majority (75%) of hackers have not seen a fundamental change in the level of difficulty in compromising privileged account credentials, despite an overall increase in IT security spending over the past two years.
Among other topics, Thycotic asked hackers how often they come across privileged account credentials – arguably the most important source of access to a network – in unprotected files like spreadsheets. Only 6% of respondents said they had never seen this, meaning 94% find privileged credentials in unprotected files at least some of the time. In fact, 50% of hackers said this is the case either “all of the time” (20%) or “most of the time” (30%) when they get their foot into the door of a network and start looking around.
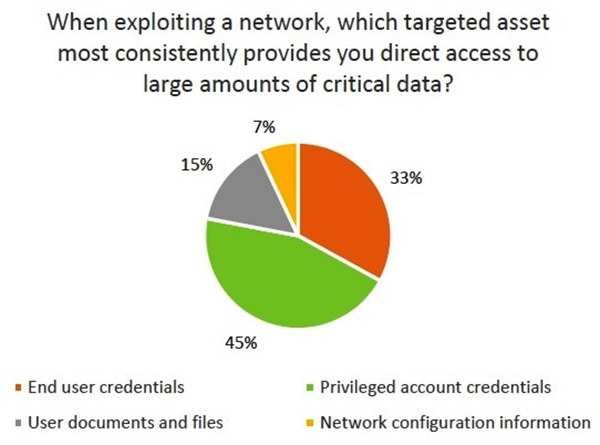
The dangers here are immeasurable, as privileged account credentials essentially serve as the keys to unlock virtually any part of the network, including mission critical data sources. The survey revealed that 45% of the hacker community identified privileged credentials as their favorite target, while only 33% chose end user credentials as the easiest way to get what they are after.
Other key findings from the survey include that:
• 9 out of 10 respondents said it is as easy - or even easier - to compromise privileged account credentials now than it was two years ago
• Healthcare organizations were indicated (29%) to be the primary target for breach vulnerability, followed by financial services companies (25%) and government organizations (24%).
It is clear from the data exposed end-user credentials still pose a major risk because they are often the first target utilized in the attack chain to gain entry-level access into the network. Using this as a foothold in the network, attackers then leverage a myriad of methods to elevate the privileges of those end-user accounts or compromise existing privileged accounts in order to gain full access to the critical data they are targeting. You can request the executive summary report here.
By MediaBUZZ


