 Cyber criminals are busy at work, especially during the end-of-year online shopping events, the security expert firm Symantec proves by detecting a major increase in attacks on online retailers and blocking almost a quarter of a million instances of attempted formjacking in the past three months.
Cyber criminals are busy at work, especially during the end-of-year online shopping events, the security expert firm Symantec proves by detecting a major increase in attacks on online retailers and blocking almost a quarter of a million instances of attempted formjacking in the past three months.
What is formjacking?
“Formjacking describes the use of malicious JavaScript code to steal credit card details and other information from payment forms on the checkout web pages of e-commerce sites. It is not a new technique, but recent campaigns are interesting as they are large, sophisticated, and have increased dramatically since mid-August 2018,” Symantec highlights by pointing out that its Intrusions Prevention System (IPS) technology proactively protects website users from formjacking attack.
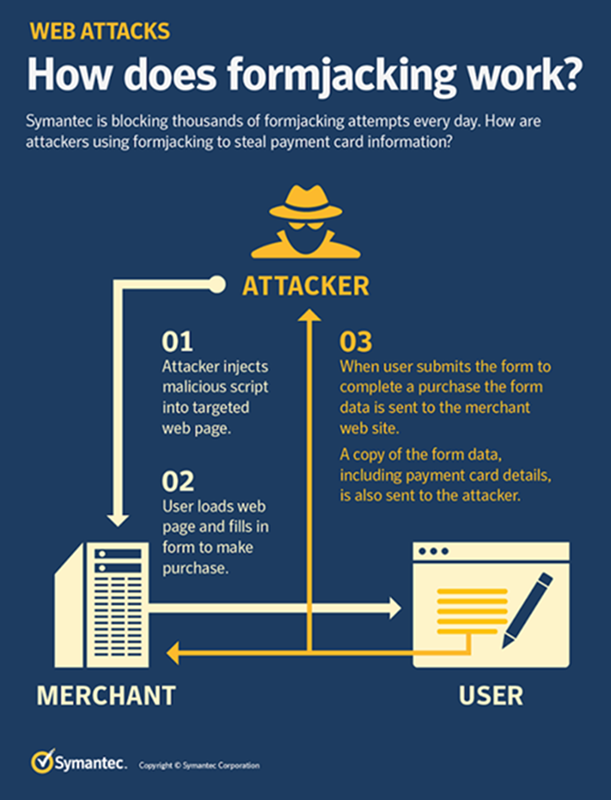
How does formjacking work?
When customers of an e-commerce site click “submit” or its equivalent after entering their details into a website’s payment form, malicious JavaScript code that has been injected there by the cyber criminals collects all entered information, such as payment card details and the user’s name and address. This information is then sent to the attacker’s servers and can be used to perform payment card fraud or be sold to other criminals on the dark web.
How do you protect against formjacking?
Victims may not realize they are victims of formjacking as their websites generally continue to operate as normal. Attackers are sophisticated nowadays and take steps to avoid detection. However, website owners should also be aware of the dangers of software supply chain attacks, as these have been used as the infection vector in some of these formjacking attacks.
The fact is that attacks can be difficult to guard against, but there are some steps that website owners can take. Symantec recommends to:
- Test new updates, even seemingly legitimate ones, in small test environments or sandboxes first, to detect any suspicious behavior.
- Use behavior monitoring to identify any unwanted patterns fast so a suspicious application can be blocked before any damage can be done.
By MediaBUZZ


